When Frontrunning is Alchemy
tl;dr
Aggregate sandwich attack statistics can be massively distorted by swaps involving low liquidity tokens. Over the last 30 days, three edge-case swaps account for roughly 99% of all estimated sandwich bot profits and 78% of user losses—despite their economic profit being close to zero.
A user swaps $1.44 of Wrapped Ether (WETH) for a long-tail token called NeuralSwap Protocol (NSWP). The fill is awful, so they open a dashboard to understand what happened. What they find is startling: the dashboard attributes a reported $1.79 million user loss to the trade—the second-largest frontrunning exploit of the last 30 days. However, the number is not just inflated, it is economically detached from reality.
As traditional financial institutions grow more interested in DeFi, it is important to properly characterize trading safety and the impact of sandwich attacks. This article illuminates that publicly available statistics do not always accurately reflect the harm done to traders, and serves as a call to action to refine and develop better methodologies.
Before we begin, it is worth noting that modeling sandwich attacks on a general-purpose blockchain, especially in low-liquidity environments, is extremely difficult. By far, the best public explorer for tracing transaction flows and understanding toxic MEV is EigenPhi.
State of the Market
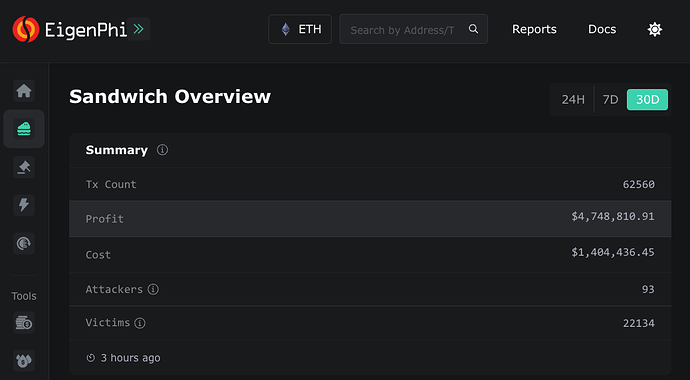
At the time of writing, 30-day profits for sandwich bots are listed at $4.749 million. The cost of these attacks—base fees burned by the protocol and tips captured by builders and proposers—is listed at $1.404 million. That should immediately feel wrong. Sandwiching is usually crowded and adversarial, if bots are keeping almost all of the upside, either market structure has changed dramatically or the accounting has gone wrong.
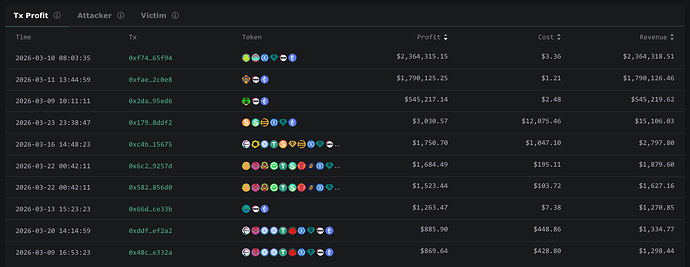
If we look at the most profitable attacks of the month, the issue starts to take shape. The top three attacks account for a combined $4.70 million in profit, while showing only $7.05 in total cost. Three bundles alone make up 99% of all reported profit.
There are plausible ways this could happen:
- Private mempools or builders could be leaking user transactions, allowing a searcher to win the opportunity without meaningful competition.
- The victim trade could arrive at the very last millisecond, leaving time for only one searcher to submit a sandwich bundle. The searcher would also have to anticipate that they have no competition and submit a low fee transaction.
- An integrated searcher—builder can purchase block proposal rights ahead of time through a preconfirmation protocol, making it the only searcher able to attack the transaction.
But in these cases, none of those explanations apply. The reality is far less spicy: these profit and loss figures are not evidence of extraordinary sandwich opportunities, but of methodological errors when analyzing low-liquidity swaps.
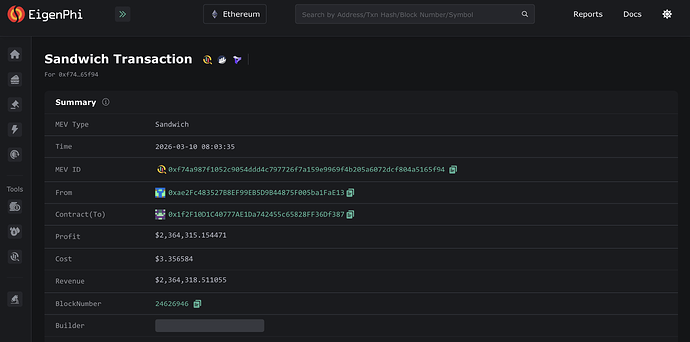
Sandwich 0xf74a - Displayed Profit of $2.36 million
This attack occurred on March 10, 2026, in block 24,626,946. The price of ether on Binance at the time of the block was $2060.50.
There were two victims. Unlike 85% of dex trades and 95% of dex volume that use private mempools to protect their transactions, both users broadcast their transactions into the public mempool [1, 2].
The first victim swapped 625 USDC and received 0.2971 ETH. Using USDC at par and Binance’s spot as a fair-value benchmark, the user should have received 0.3033 ETH. In reality they got 0.2971 ETH. This is an approximate loss of 2% or $13.
The second victim sold 0.048554 ETH, valued at approximately $100, for a long-tail token called SAIYAN; they received 416.76 tokens in-exchange. If we re-simulate this transaction at the top of the block—effectively removing the frontrun, they would have received 429.65 tokens instead. This reflects a user loss of 3%, or $3.
Combining the two victims, the user losses were approximately $16 in total. Nowhere near the $2.36 million suggested by the explorer.
Where does the profit come from? The backrun transaction routed two trades through cowfarm finance (COW) pools. The first swap left the bot with 0.000473 COW and the second swap paid 0.499998 USDT for 0.000000000100015488 COW—implying a value of $4.999 billion for each COW token. The explorer then uses the details of the final swap to mark the remaining COW tokens at $2.364 million.
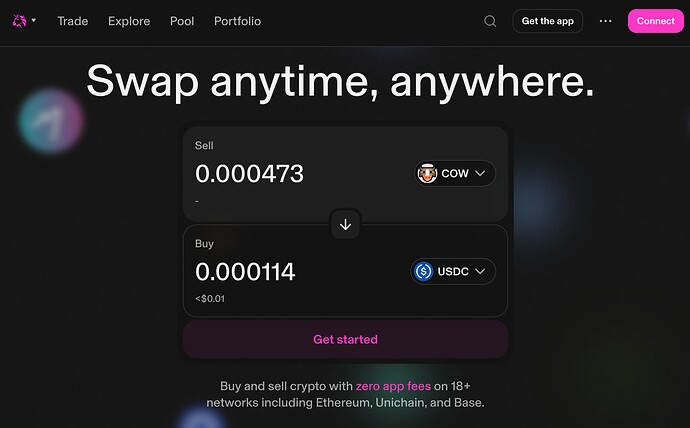
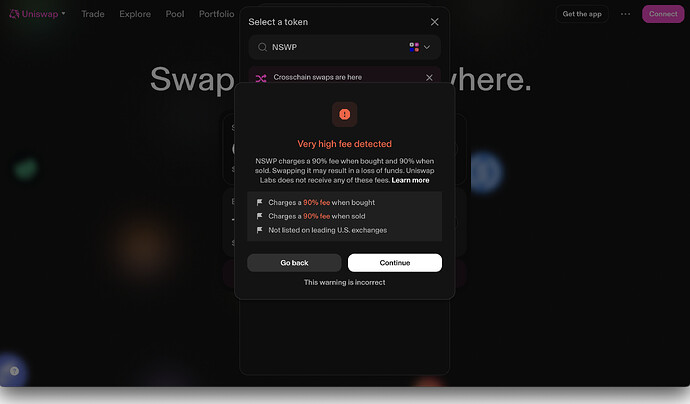
If we try to swap these tokens on Uniswap right now, we get a honeypot warning and an estimated value of less than one cent. The displayed profit is not reflective of reality and certainly should not be treated as a user loss.
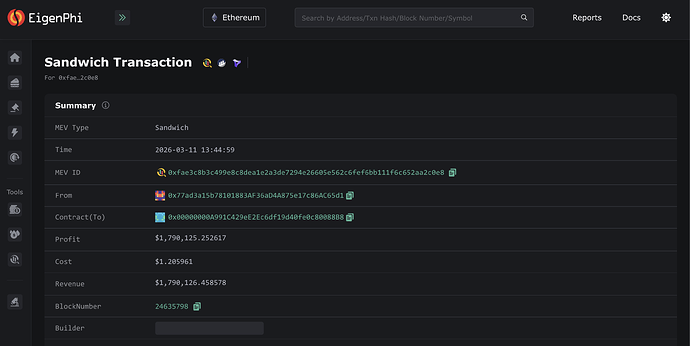
Sandwich 0xfae3 - Displayed Profit of $1.79 million
This attack took place on March 11, 2026 in block 24,635,798. The price of ether on Binance at the time of the block was $2083.54. There was only one victim and their transaction was broadcast to the public mempool.
First, the attacker frontran the victim by swapping 9.6481 WETH for 74,009 NSWP. Using the Binance price, this implies an entry price of 0.00013036 WETH per NSWP, or roughly $0.2716 per token.
Next, the victim’s trade landed. The user sent 0.0006897 ETH, about $1.44, to the Uniswap V2 Router. Uniswap minted an equivalent amount of WETH and then swapped it for 0.0000005764 NSWP. Using the attacker’s average price as a reference, the NSWP was worth about $0.000000157. This was a catastrophically bad fill, the user’s loss was essentially 100%.
Finally, the attacker swapped back 7,400 NSWP to cover its buy-in; receiving 9.6487 WETH back—an implied valued of $2.72 per NSWP per token. The attacker only received 0.000585 WETH more than it initially spent, worth roughly $1.22. The gas cost of the two swaps was also $1.22, making the attacker’s realized cash profit approximately zero.
The explorer shows that the attacker retained 66,608 NSWP after the swaps. Marked at the same $2.72 exit price, these tokens would be worth $181,173. This is 10x less than the displayed profit–it is also a clue.
If you try to place a NSWP swap on Uniswap, it flags that the contract charges a 90% fee on all trades. If we inspect the logs for the transaction, we see that the actual swap was not actually 7,400 NSWP but in reality 740 NSWP —explaining how the profit got logged at nearly $1.8 million.
If we go one step further, we realize that 7,400 is approximately 10% of the purported 74,008 tokens received by the bot in the first swap. Checking the bot’s balance directly after the swaps—and validating by checking the current holders and the historic transfers of NSWP, we see that the bot only retained dust tokens from the attack.
The profit from this attack was $0 and the user loss was at most $1.44.
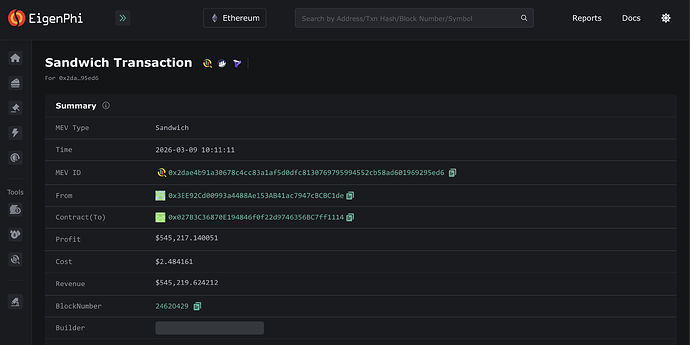
Sandwich 0x2dae - Displayed Profit: $545 thousand
This attack took place on March 9, 2026 in block 24,620,429. The price of ether on Binance at the time was $2015.66. There was only one victim and their transaction was broadcast to the public mempool.
The victim swapped 0.002 ETH, valued at $4.03 for URS Virtual Currency (URSVC). They received 0.0000000092522686 URSVC. At the time, this was only the fifth ever trade of the token; since the attack there has only been one additional trade.
Immediately before the transaction, the attacker spent 270 WETH to acquire over 15 trillion URSVC tokens. Liquidating the tokens after the user’s trade, EigenPhi displays that the attacker had a net gain of 0.000093 ETH as well as 15,736,666,881,390 URSVC.
The size of the frontrun was 270 ETH, or approximately $544 thousand per Binance’s price, which is where the displayed profit comes from. However, inspecting the list of swaps and current holders on Etherscan it seems like the backrun actually sold the vast majority of the URSVC and that EigenPhi missed it.
The bot’s realized profit was $0.19 and some illiquid tokens. Certainly not a profit or user loss of half a million dollars.
So What?
The aggregate overstatement from these three attacks is approximately $4.70 million. Repricing these outliers would reduce the displayed average sandwich bot profit for the past 30 days from about $76 per attack to under $1, and lower the implied average price impact per sandwiched trade from roughly $98 to $22.
On that same basis, the implied price impact relative to the past 30 days of Ethereum L1 dex volume would fall from about 1.53 bips to 0.37 bips.
Although this analysis only examines three sandwich attacks, it shows that public dashboards can materially overstate sandwich profits and trader harm in low-liquidity edge cases. As defi trading comes under more scrutiny from regulators and financial institutions, we need better standards and more robust measurement techniques to illuminate the dark forest.