Timing Games: Probabilistic backrunning and spam
TL;DR
We discuss the main results from our new paper Timing Games: Probabilistic Backrunning and Spam. We model searchers’ competition to optimistically extract MEV. More specifically:
- We model probabilistic searching as a timing game under delayed observability: searchers want to have the first transaction after a random arrival time T of an opportunity.
- The game has a unique symmetric Nash equilibrium (for n\ge2), and in that equilibrium everyone has zero expected profit: competition dissipates the opportunity value into fees (or other infrastructure costs).
- The equilibrium strategy has a simple shape: randomize the first probe, then follow a deterministic successor rule for all later probes.
- Total spam is approximately V/c for any number of competitors n\geq 2: roughly “expected value per opportunity divided by per-tx cost”.
- We discuss negative externalities of spam, mitigations and open problems.
Joint work with @Christoph and @kakia. Thanks to @boz1 and @willwoo for valuable feedback and discussions.
Introduction
Backrunning is usually described as reactive: searchers observe a state change (a DEX swap that moves a price, an oracle update that triggers liquidations), detect an opportunity, and immediately submit a transaction or bundle of transactions to exploit it. In this classical model, the “search” happens off-chain (mempool/state monitoring), and the on-chain transaction mostly just checks whether the opportunity is still there and executes it.
That picture fits Ethereum-like settings, where searchers can often observe pending order flow—through public mempools or order-flow-sharing systems such as MEV Blocker and MEV-Share—and race to backrun newly revealed opportunities. On some other L1s, and especially on many L2s, the environment looks different: blockspace is cheaper, pending transactions are less visible or private by default, and some sequencing designs offer little or no revert protection, so transactions accepted for sequencing may still be included even if they later revert at execution time. In those settings, waiting for an opportunity to become public and then reacting is less effective. Searchers can instead move part of the search on-chain, submitting probe transactions that execute profitably only if the relevant condition is true at execution time, and otherwise revert or fail without changing state.
Pseudocode of on-chain searching contract:
contract ProbeExecutor:
function probe(params):
state = read_relevant_state(params)
profit = estimate_profit(state, params)
if profit > tx_cost + margin:
execute_strategy(params) // arb / liquidation / backrun
A searcher can submit this same probe at times t_1 < t_2 < t_3 < ... during the block interval. Each transaction “searches” at execution time. If the opportunity appears after t_2 but before t_3, then the probe at t_3 is the first one that can monetize it; earlier probes revert because they arrived too early, and later probes arrive too late. Probing therefore buys coverage over possible arrival times.
That shift changes the nature of the MEV game on L2s . It’s no longer about “reacting fastest” or “bidding the most” to win. Instead it becomes a timing game under uncertainty: an opportunity may occur during the next block interval, but the exact moment (and position in the block) is uncertain and only becomes observable after the block is released. So searchers face a strategic dilemma:
- They can wait until the opportunity is confirmed, at the risk of someone else already being positioned right after it.
- or spam multiple probes to cover many possible “positions in time”, paying fees for each attempt.
This raises a different strategic problem. Searchers are choosing an entire schedule of attempts, balancing coverage against probing costs. When should the first probe be sent? How should later probes be spaced? How many probes are worth paying for?
Model & Results
We propose a game to formalize these incentives and characterize the unique symmetric equilibrium.
Timing Game
There are n risk-neutral searchers that try to extract an MEV opportunity of net expected value V that realizes at a random time T\in[0,1] with an absolutely continuous distribution G. Time t=0 represents the moment when the previous state update (i.e. Blocks, Flashblocks, Solana Shreds, etc) has been released, and t=1 is the moment when the next state update will be released. Each transaction has a fixed cost c>0, and transactions are ordered by a First-Come First-Serve (FCFS) rule.^1 Each searcher can send multiple transactions at any time. The opportunity is captured by the searcher whose transaction is the earliest one after T. Ties are broken uniformly at random. If no one has sent a transaction after T, assume the opportunity is extracted through a top-of-block auction and effectively disappears^2 for the searchers.
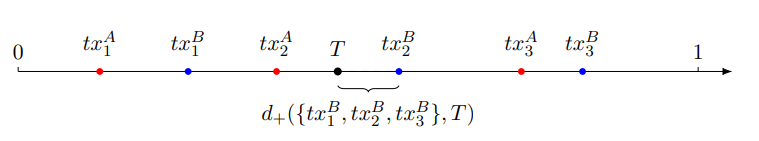
Game with players A and B. Player A’s transactions are shown in red, and player B’s transactions in blue. T denotes the arrival time of the opportunity. In this arrangement, both players place 3 transactions and player B wins the opportunity.
With this model in mind, we can reformulate the previous vague questions as:
- What is the set of (symmetric) Nash equilibria?
- How many total transactions are sent in equilibrium?
- When are the probes send?
A very natural first guess (by any researcher, human or AI) is that players use a homogeneous Poisson process with some intensity rate \lambda>0. However, this cannot be a Nash equilibrium. The intuition is simple: after sending a transaction at time t, there is no incentive to send another one “too soon” after t, because the extra probability of being first-after-T is too small to justify paying another cost c. But a Poisson process puts (with positive probability) two actions arbitrarily close together.
Main theorem (Informal)
Our main result is that (as long as there are at least two competitors) this timing game has a single symmetric equilibrium, which has a very particular shape.
Theorem 3.1 For n\geq 2 and c\in(0,V):
- Unique symmetric equilibrium. There is a unique symmetric Nash equilibrium.
- Zero expected profit. In that equilibrium, each searcher’s expected payoff is 0.
- Simple equilibrium structure. Each player’s strategy can be described by two objects:
- a distribution for a single random draw X (the time of searcher’s first probe, or X=+\infty if searcher does not participate), and
- a successor map \psi(\cdot) that tells a searcher when to send their next probe given their previous one.
Concretely: draw X, send a probe at time X, then (if X\le1) send follow-ups at
until time t=1. A key intuition is that probes are never “too close” nor “too far” apart: once you’ve probed at time x, probing again almost immediately is usually redundant, because the extra chance of being first-after-T is too small to justify paying another c.
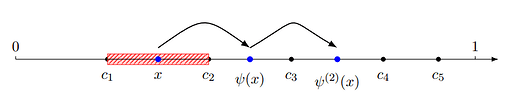
The picture below gives a good intuition: the only randomness is in the first draw X (red hatched region). After that, the next probe is a deterministic jump forward given by \psi, and repeating \psi generates a whole “schedule” of probes.
Total Spam
The equilibrium also predicts how much spam the competition generates.
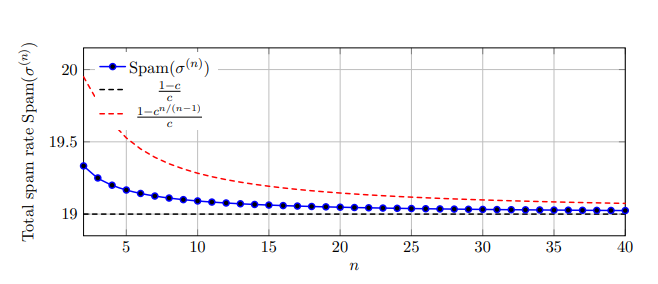
Let \text{Spam}(\sigma) be the expected total number of transactions (across all n searchers) sent during the block interval. In the unique symmetric equilibrium,
In particular, as the number of searchers increases,
So when c is small relative to V, spam scales like V/c. Interestingly, more searchers do not necessarily mean more total spam (the equilibrium spam can be non-monotone in n), but as n\to\infty the total spam converges to \frac{V}{c}-1.
Interpreting c as a transaction fee, this also says the total fees paid are close to the opportunity value: in equilibrium players make zero expected profit, and competition converts (almost all of) the prize into fees, and the sequencer revenue c\cdot\text{Spam}(\sigma) is between roughly V-c and V.
Wat do (A mechanism design perspective)?
Is on-chain probing bad? Not in the same way as classical spam: probe senders pay fees, so the cost is at least partly internalized by searchers. But it still creates meaningful negative externalities. In an ideal world, we’d prefer blocks to be filled with value-bearing user transactions rather than random attempts to extract MEV which increases congestion, raises infrastructure and operating costs for sequencers and RPCs, and reduces users’ welfare. On PGA-style chains, probes directly compete with users with low- to mid-value transactions under the same fee as the transaction that generates the MEV opportunity. Thus, in the worst case, when blockspace has high demand, probing transactions can crowd out useful activity and lower welfare. In FCFS regimes the effect can be even more disruptive: bursts of probing can delay high-value, time-sensitive transactions (liquidations, hedges, user swaps) simply because they arrive during a congested period. Finally, probing weakens transparency around MEV leakage. When value is extracted through many small probe transactions rather than an explicit payment (as in an order-flow auction), the fees mostly accrue to the sequencer while applications and users see the downside: more congestion, worse execution, and a harder time designing mechanisms that return value to the apps or the users. So, there are good reasons for trying to mitigate spam.
The model is intentionally stylized, but it helps organize mitigation ideas. In the timing game, spam is rational when (i) probes are cheap relative to the opportunity expected value, (ii) the targets are predictable and valuable, and (iii) there is a long enough “uncertainty window” to cover with random attempts. That suggests three broad directions:
- Increase Fees The simplest mitigation is to increase the per-transaction^3 cost c (e.g., by raising the base fee). This reduces spam mechanically, but it comes with a clear trade-off: it prices out agents with lower valuations and does not distinguish where the demand comes from, because everyone pays more even if only a few contracts are being spammed.
- Local fee markets are more granular: they isolate the dimension where congestion is concentrated and price that dimension more aggressively while keeping everything else cheap. Concretely, you can imagine dynamically adjusting fees for transactions that touch specific “hot” contracts, so the marginal cost rises exactly where probing creates the most externalities.^4
- Minimize MEV leakage In practice, a large share of this spam tends to come from a small number of opportunity types—especially cyclic arbitrage and backrunning of predictable oracle updates.
- For cyclic arbitrage, a natural mitigation is better on-chain routing by DEXs and aggregators: if an opportunity is worth spamming for, then (as a rule of thumb) it’s also worth computing and executing the best route on-chain on average, because the arbitrage and routing are essentially equivalent optimization problems.
- For oracle-driven opportunities such as liquidations, updates can be (somewhat) predictable, which creates specific blocks with high incentives for probing. One mitigation is to move toward off-chain order-flow auctions at the oracle update, i.e., auction the right to be the first transaction after the update and include the winner of the auction after the oracle update. This has two upsides: it reduces spam, and it helps internalize value that would otherwise leak to the sequencer through spam.
- Information release One driver of spam is the amount of extractable value available per unit of time. If blocks are shorter, or information is released more frequently, less value may accumulate between opportunities to act. When that reduces the value extractable over a fixed period, it also reduces the incentive to fill blocks with probes.
More frequent information release can, however, shift competition from spam to latency: when the uncertainty window shrinks, being fast matters more. In FCFS settings, that likely increases incentives to invest in infrastructure/latency races and can reduce chain revenue from spam fees (because less spam is sent), even if it improves the user experience. Thus, there is a clear trade-off.
Conclusions
When blockspace is cheap and visibility is delayed, rational searchers may compete by sending probabilistic probes rather than waiting for certainty. In our model this turns MEV extraction into a timing game with a unique symmetric equilibrium:
- Unlike a Tullock contest, but akin to first-price and all-pay auctions with homogeneous players, players make zero expected profit in equilibrium (competition dissipates the value).
- Equilibrium behavior has a simple recursive structure (random first probe, then deterministic follow-ups).
- Total spam grows on the order of V/c, meaning the sequencer can capture most of the opportunity value through fees when c\ll V, at the cost of filling blocks with economically meaningless traffic.
Open Problems
We end the paper with several open problems. First, while our simulations (see previous Figure on total spam) show that spam is strictly decreasing in the number of players, and we prove it is non-increasing, a full mathematical proof of strict monotonicity remains open.
Second, the analysis in the paper focuses on symmetric equilibria. Asymmetric equilibria exist, but we do not characterize them here. Although parts of our proofs rely on symmetry, we expect the zero expected payoff conclusion to extend to asymmetric equilibria analogously. What remains open is the full characterization of the set of asymmetric equilibria.
Third, it remains open to analyze the same game with heterogeneous players. What changes when searchers differ in costs, latency, or expected values V_i? For heterogeneous values, we conjecture an analogue of all-pay auction outcomes: higher-valuation agents may capture surplus relative to the second-highest valuation, but the exact equilibrium structure is unresolved. For heterogeneous latency, pure speed advantages are less relevant within the probing window (a faster agent can often simply start earlier), but they matter once we allow reaction advantages—in particular, when all probes miss the opportunity and the game effectively shifts to “who can react first” after the miss. This extension likely preserves the main qualitative conclusions, but it is interesting because it can capture mechanisms like TimeBoost.
References
- Bruno Mazorra, Christoph Schlegel, and Akaki Mamageishvili. *Timing Games: Probabilistic backrunning and spam. February 25, 2026.
- Ozan Solmaz, Lioba Heimbach, Yann Vonlanthen, and Roger Wattenhofer. *Optimistic MEV in Ethereum Layer 2s: Why Blockspace Is Always in Demand. 2025.
Footnotes
- This applies to blockchains with transaction fee mechanisms that either order all transactions by time of arrival (FCFS blockchains) or order transactions with identical priority fees by timestamp. The latter case applies when all searchers bid only the base fee and the chain’s tie-breaking rule relies on timestamps.
- This is just a modeling choice to avoid edge cases: if nobody has any transaction after T, we assume the opportunity is captured by someone else (e.g., the sequencer/validator via a top-of-block auction) and is therefore unavailable to the searchers.
- Recently Base and Arbitrum raised fees to reduce spam.
- One concrete implementation is a “pay-for-reading” model: for contracts that searchers repeatedly probe to extract optimistic MEV, charge a tiny fee whenever a transaction reads state variables. This increases the marginal cost of probing (so it reduces spam), and it lets the application/protocol capture some of the value that would otherwise leak into sequencer fees. This model could be combined with multidimensional fee mechanisms, with the surplus generated on top of base fees distributed among protocols.