Jovay: Blockchain Infrastructure for Asiaʻs Institutional Finance
A deep dive into Jovay Networkʻs technical architecture and what it reveals about the tradeoffs necessary to comply with Asia regulators
1. An L2 Built for Regulated Finance
In November 2025, Towngas (Hong Kong and China Gas Company), a publicly listed utility with over 150 years of operating history, announced a HK$100 million credit facility backed by tokenized energy infrastructure assets.[1] The underlying collateral: natural gas distribution networks, solar and wind projects, energy storage systems, and carbon credits. The entire deal settled on Jovay Network, a layer 2 blockchain that had gone live on Ethereum mainnet just two months earlier in September.
The Towngas deal was not an isolated case. In a separate project, Ant Digital (“Ant DT”), the digital technology subsidiary of Ant Group, tokenized the cash flows from electric vehicle charging networks across Asia. The structure used SPVs that held operator contracts, while token holders received a proportional share of charging fee revenue. Investors completed KYC through ZAN, Ant DTʻs compliance platform, and the tokens were restricted to allow-listed addresses. Settlement occurred on Jovay, enabling transfers across jurisdictions where traditional cross-border security transactions can take days.[2]
For institutional blockchain, these projects were significant. A century-old listed company tokenizing a regulated credit facility and RWA tokenization leveraging Ethereumʻs finality – both projects running on Ant DTʻs infrastructure.
Jovay is built on the thesis that Asia’s regulated financial institutions don’t need blockchain to be permissionless; blockchains need it to be compliant by design and institutions are willing to accept significant trade-offs in decentralization to get there.
2. Hong Kongʻs Sandbox
While Jovayʻs parent company, Ant Group, is based in China, it is Hong Kongʻs regulatory environment that is driving Jovayʻs institutional strategy.
Hong Kong has made a deliberate, government-led bet on becoming Asia’s digital asset hub. The HKMA launched Project Ensemble in March 2024 — a regulatory sandbox for tokenized asset experimentation using tokenized deposits and wholesale CBDC as settlement rails.[3] By November 2025, the program graduated from sandbox to live pilot: EnsembleTX, with participants including HSBC, Standard Chartered, Bank of China (HK), BlackRock, and Franklin Templeton, running real-value transactions in tokenized money market funds and real-time treasury management.[4] The SFC has been co-leading tokenization initiatives for the asset management industry in parallel, developing regulatory guidance for compliant secondary trading of tokenized securities under its existing Type 1 and Type 9 licensing framework.[5]
Hong Kongʻs regulators are setting their own regional blockchain policy, and are proactively deciding which blockchain they will trust. Jovay is purpose-built to be the answer for the Asia-Pacific institutional segment — with a specific bet that Ethereum-anchored settlement, local regulatory alignment, and Ant Group’s enterprise relationships create a more defensible position than either global crypto-native L2s or consortium chains built by Western banks.
3. Jovayʻs Customers – And What They Actually Need
Jovay is not primarily targeting the same customers as general-purpose L2s such as Base, Arbitrum, or OP Mainnet. Its focus is narrower: regulated financial institutions and enterprises, especially in Hong Kong and similar jurisdictions, that want to tokenize real-world assets within formal compliance frameworks. Hong Kong’s own regulators are actively encouraging tokenization through initiatives such as Project Ensemble and the broader HKMA tokenization agenda.[6]
Jovayʻs architectural choices are responses to institutional constraints rather than as attempts to maximize decentralization.
Problem 1: Unpredictable Finality
Optimistic rollups impose 7-day challenge windows before withdrawals are final. For securities settlement operating on T+0, T+1, or T+2 cycles, a multi-day uncertainty window is difficult to reconcile with institutional settlement requirements. [7]
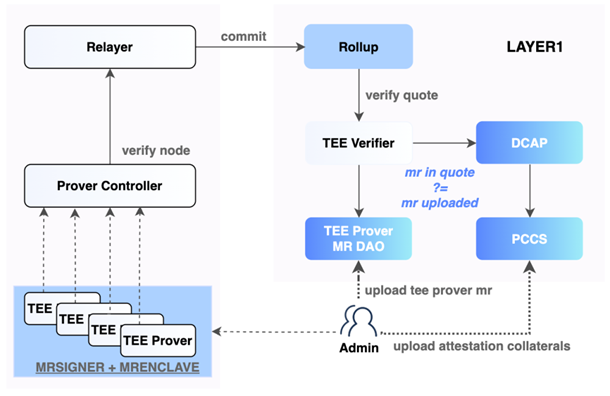
Jovay’s response: Ethereum-anchored batch verification with TEE-backed state verification. Jovay records batch commitments, state roots, and message roots on Ethereum, commits batch data through blobs, and finalizes withdrawals on L1 after inclusion is proven. Today, the verification path uses TEE proofs, while ZK verification hooks exist in the codebase but are not yet active. That gives Jovay a faster finality profile than optimistic rollups, but the current trust model still depends on TEE assumptions rather than end-to-end cryptographic validity proofs. [8]
The trade-off: Faster than optimistic rollups, but trust depends on TEE assumptions, not end-to-end cryptographic validity proofs.
Problem 2: Ordering Opacity and MEV
Institutions require execution that is deterministic, reproducible, and auditable. Public mempools and fee-priority ordering can create front-running and adversarial ordering risks that may be acceptable in DeFi but are not tolerable in regulated securities markets.
Jovay’s response: Centralized sequencing with deterministic execution rules. Block execution is based on inferred write sets, with transaction order preserved within groups as they appear in the block and retries conflicts serially in block order.[9, 10] This makes execution more reproducible and auditable than priority-fee ordering.
The trade-off: Public-mempool-style MEV exposure is reduced, but censorship and operator-trust risk increase as ordering power is concentrated in the sequencer.
Problem 3: Regulatory Ambiguity
Many general-purpose public L2s are designed for open participation rather than institution-first compliance. Even where a sponsoring entity exists, regulated institutions may still face gaps around formal operator accountability, contractual SLAs, incident response, and supervisory escalation compared with permissioned or operator-led infrastructure. For institutions operating under SFC licensing or HKMA regulatory frameworks, this creates an unacceptable compliance and liability gap.
Jovay’s response: Permissioned operational roles with clear legal accountability. Ant DT operates the sequencer, prover, and relayer infrastructure under defined governance controls. Upgrade paths require multi-sig authorization from the operational team. Institutions know who they are dealing with and can hold that party accountable under contract and law. [10, 11, 12]
The trade-off: Accountability is contractual and reputational, not cryptoeconomic. Institutions are trusting Ant DT as a counterparty and not a trustless system.
Problem 4: DeFi Composability as Compliance Risk
For tokenized securities, open composibility can be a liability as well as a benefit. The more freely assets move across DeFi protocols, the harder it becomes to preserve transfer restrictions, investor qualification rules, and compliance controls. Compliance requires controlled composability, not permissionless interoperability.
Jovay’s response: A more controlled operating model around issuance, bridging, and settlement. Jovay is a system with operator-managed bridges, relayer-based message delivery, and privileged controls rather than unrestricted permissionless interoperability. DT-TAAS provides protocol-level transfer restrictions via smart contract templates and ZAN Identity supplies KYC verification and a compliance stack that enforces protocol-level investor qualification rules. [8, 13]
The trade-off: Controlled composability limits secondary market liquidity. Assets cannot freely move across DeFi venues, which constrains the depth and breadth of available counterparties.
Problem 5: Operational Complexity
Running blockchain infrastructure requires crypto-native expertise. Most institutions want SLAs, incident response, and a commercial counterparty they can call when something breaks. They do not want to operate nodes, manage relayers, participate in governance, or upgrade processes.
Jovay’s response: Managed architecture with no requirement for institutional users to operate public validator infrastructure. Jovay uses Ethereum for settlement anchoring, proof verification, and withdrawal finality, while keeping operational responsibility with relayers, privileged owners, and other managed components. The result is a more enterprise-style operating model.
The trade-off: Institutions avoid infrastructure complexity, but they rely more heavily on relayers, privileged operators, and Jovay’s current verification architecture rather than inheriting Ethereum’s security in a complete sense. [10]
4. Jovayʻs Technical Architecture: What Was Built and Why
1. The Proof System – From Trusted to Trustless
Jovay’s most consequential architectural decision is its phased proof approach: TEE-based verification live on mainnet today; ZK proofs on the roadmap.[8] TEE verification using Intel SGX/TDX attestation was a deliberate engineering and business decision for several reasons.
- Speed to market. Building a production-ready ZK prover for general-purpose EVM execution is a multi-year effort. Launching with TEEs allowed Jovay to hit mainnet in September 2025 with audited, production-grade verification rather than waiting for zkVM proving technology to mature.[14]
- Cost. ZK proof generation for complex state transitions is orders of magnitude more computationally expensive than TEE attestation. At current ZK proving costs, high-frequency institutional trading workloads would make the fee structure unworkable. TEE proving completes complex state transitions in seconds while ZK proofs take minutes with todayʻs hardware.[8]
- Institutional familiarity. Financial institutions already deploy TEEs in existing infrastructure — HSMs, secure enclaves for key management, and confidential computing. For institutional risk managers, the known risks of TEEs are safer than the unknown risks associated with newer cryptographic ZK proofs.
TEEs introduce physical hardware trust assumptions and a documented history of side-channel vulnerabilities — Plundervolt, SGAxe, CacheOut — requiring ongoing Intel patches and an assumption of supply chain integrity.[15] A compromised TEE enclave could, in principle, produce fraudulent state transitions that L1 would accept, because L1 is verifying the attestation, not the mathematical proof. Jovay’s OpenZeppelin and SlowMist audits cover the verifier contract logic and enclave measurement governance, but they cannot audit Intel’s hardware.[14, 16]
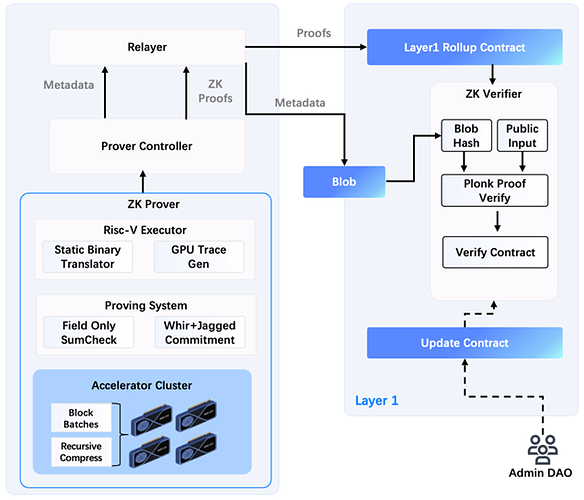
Jovay’s roadmap includes transitioning to ZK validity proofs (zkSNARK-style arguments) with a zkVM-like approach that proves DTVM execution traces. Adding ZK proofs eliminates the hardware trust assumptions required of TEE proving and provides cryptographic validity further strengthening security guarantees for regulators. It also aligns with Vitalikʻs Ethereum roadmap where ZK proving is the standard.
Ant DTʻs ZK research has yielded several technical innovations: [17]
- Packed Sumcheck over small-characteristic fields: Published in AsiaCrypt 2025, this research demonstrated 2-5x speedups for financial computation circuits.
- Hardware acceleration: GPU cluster acceleration achieves more than 20x Sumchecks speedup over CPU baselines. Static binary translation delivers 10-100x execution speedups.
- Multi-sized chip batch processing: Reduces computation complexity by adding chips to Sumcheck execution when trace sizes match.
- WHIR Scheme for polynomial commitment: More than 40% efficiency gain over standard approaches.
- Table-based rotation overhead reduction: Converts linear rotation to constant via table construction and lookup.
Combined with access with Alibabaʻs cloud infrastructure and hardware resources, Jovay is poised to be a leading ZK proving operator. What remains unresolved is the timeline and the governance question: when ZK proofs replace TEEs, will Ant DT retain the same degree of operational control that institutional customers require?
2. Parallel Execution – Performance Architecture
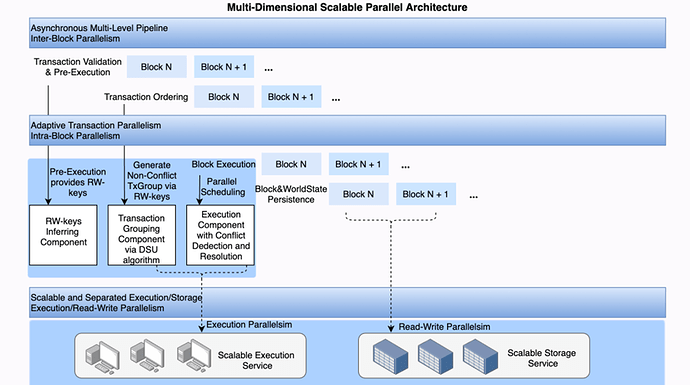
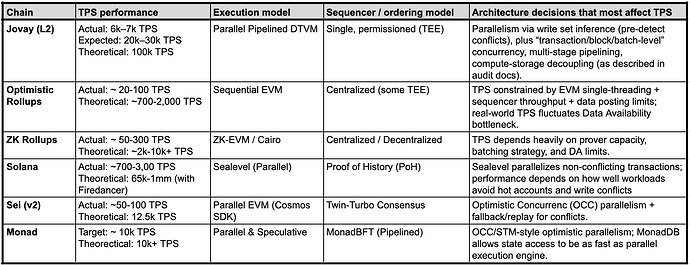
Traditional EVM processes transactions sequentially, creating artificial throughput ceilings regardless of available hardware. Jovay implements a three-tier parallel execution pipeline similar in concept to Solanaʻs optimistic parallelization:
- Static dependency analysis: Each transactionʻs read/write sets are preprocessed and transactions touching independent states – different accounts, different contracts – are marked parallelizable.
- Optimistic concurrent execution: Parallelizable transactions execute speculatively and concurrently. Conflicts (two transactions writing to the same state) trigger an abort and re-execution of one.
- Deterministic ordering maintained: Despite parallel execution, canonical ordering is deterministic and reproducible — which matters for financial audit trails.
Benchmark materials report 6–7k TPS for single nodes and 22–30k TPS in multi-process configurations, with a stated 100k TPS target.[17] These should be read as execution-layer benchmarks under controlled conditions, not sustained settlement throughput under mixed institutional workloads. The same audit materials note that background or mixed loads achieve only 240–260 TPS — the bottleneck shifts to contract logic complexity under realistic conditions.
The more binding capacity constraint comes from Ethereumʻs data availability layer. Jovay currently posts transaction data to Ethereum via EIP-4844 blobs.[18] Under post-Fusaka limits with 14 blobs per block at 10:1 compression and 200 bytes per transaction, the sustainable throughput ceiling is roughly 7,400 TPS at target blob capacity and 11,100 TPS at maximum blob capacity. For a Towngas credit facility or an EV charging infrastructure SPV, this is more than sufficient. For securities order matching at traditional exchange scale (100k - 1million TPS), Ethereumʻs global blob capacity is a meaningful ceiling.
Jovay uses blobs strictly for data availability during the window where the network needs to fetch, verify, and resolve state transactions. The team is currently implementing a feature to reconstruct L2 state from L1 data, providing a trust-minimized way to rebuild state for users without an existing L2 database.[19]
3. The Compliance Stack
The architecture that matters most for Jovayʻs institutional customers is not the proof system or the execution engine, but the compliance integration.
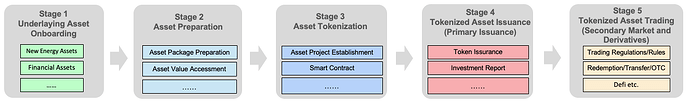
Real-world assets go through a five-stage lifecycle:[8, 10]
- Asset onboarding (AntChain / AntChain Bridge): Due diligence; legal structure; SPV creation through AntChain.
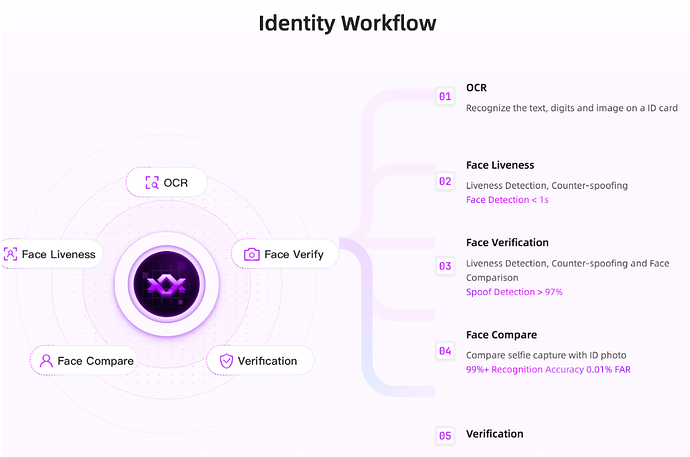
- Preparation (ZAN): KYC documentation; investor qualification criteria; transfer restriction rules; cryptographic anchoring via Merkle proofs or ZK commitments; SPV-like asset packaging.
- Tokenization (DT-TAAS): Smart contract deployment with embedded access controls.
- Primary Issuance (Jovay): Initial token distribution to licensed institutions and qualified investors on the Jovay chain; verified investment reports on-chain; cap table initialization.
- Secondary Trading (Jovay): Compliant secondary market transfers with protocol-level restrictions enforced; programmable access controls; verifiable on-chain settlement.
Zan, Ant DTʻs compliance platform, handles eKYC, AML screening, and KYT (know-your-transaction) real-time risk scoring. ZAN maintains private PII data off-chain while Jovay posts transaction data to Ethereum for public auditability.[13] Regulators can verify compliance without exposing user data on a public ledger. This architecture is a direct response to Hong Kong SFCʻs requirements for compliant tokenized securities trading.
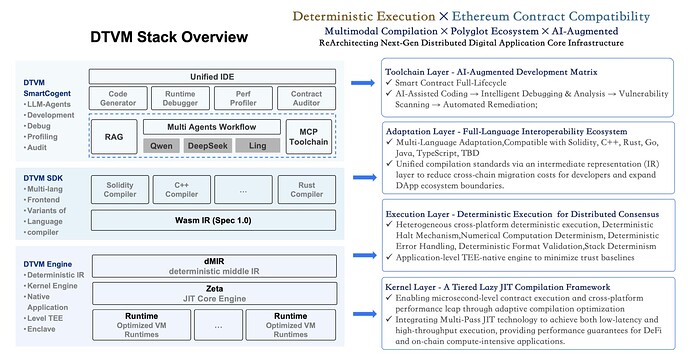
The Deterministic Virtual Machine (DTVM), Ant DTʻs WASM-based execution framework, is currently in development and is not yet on testnet or mainnet. [19, 20] The current mainnet stack runs EVM JIT. DTVMʻs core architecture with WASMʻs cleaner execution semantics makes it more amenable to ZK circuit construction than EVM bytecode.[21]
Itʻs core design includes: [21, 22]
- Compilation: Hybrid lazy-JIT (ZetaEngine) with two tiers of function-level granularity:
- FLAT mode: Fast compilation for quick startup, dedicated physical reigster for gas.
- FLAS mode: Aggressive optimization for long-running contracts, sophisticated register allocation.
- Determinism: dWASM (deterministic WebAssembly) specification ensures identical execution across nodes regardless of JIT timing/optimization.
Key innovations include:
- dMIR: Deterministic Middle IR intermediate layer enabling mode-agnostic optimization ensuring identical execution across all nodes.
- Zero-overhead memory protection: CPU hardware memory protection (virtual memory + MMU) not software bounds checking. Each WASM instance gets 8GB virtual address space with guard pages.
- Gas metering integration: JIT-compiled gas-tracking — FLAT mode uses dedicated physical register; FLAS mode uses virtual registers with compiler optimized spills.
- AI integration: SmartCogent toolkit — LLM-powered contract development, debugging, security auditing (81% vulnerability detection, 86% auto-repair).
- Faster startup performance: 22-58x faster startup vs Wasmtime / Wasmer. For institutional workloads with many short-lived contract interactions, startup latency matters more than maximum throughput.
Once Ant DTʻs transition to ZK proofs is complete, DTVM is the execution layer that makes it tractable at institutional throughput levels.
Jovayʻs on-chain privacy includes cryptographic smart contract features that conceal transaction details – addresses, amounts, and balances – while maintaining verifiability. These features are enabled at the smart contract layer through precompiled contracts that provide the necessary cryptographic primitives. The privacy stack prevents information leakage and front-running while allowing regulators to verify compliance.[19]
5. The Ecosystem Stack – Vertical Integration is Strategic
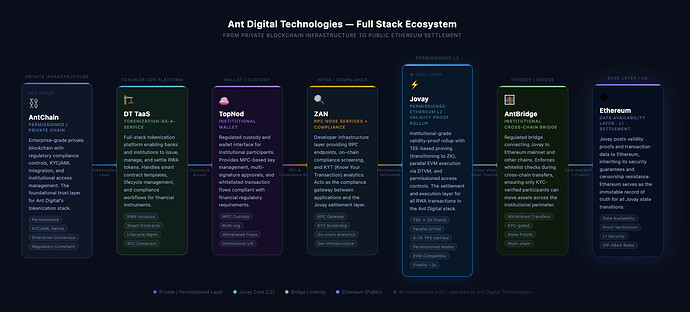
Jovay is not a standalone chain. It is the settlement layer in a vertically integrated product stack that includes DT-TaaS (tokenization-as-a-service), ZAN (compliance and identity), TopNod (self-custodial consumer wallet), AntChain (permissioned private chain for sensitive enterprise data), and AntChain Bridge (cross-chain messaging between private and public layers).[13, 23, 24, 25]
This vertical integration is Jovay’s actual competitive strategy. When a Hong Kong asset manager tokenizes a real estate fund, they don’t need to assemble a compliance stack from multiple vendors, integrate a separate KYC provider, build their own smart contract templates, and find a self-custody wallet for distribution. Ant DT offers all of those services as a single commercial relationship, under SFC/HKMA-aligned compliance frameworks, with Ant Group’s institutional relationships as the backstop.
6. The Trade-Offs – What Jovay Gave Up
1. Credible Neutrality
Without a native token, without an open validator set, without slashing mechanisms, the security model relies on Ant DT’s institutional reputation, contractual accountability, and operational integrity rather than cryptoeconomic incentives.[8] This is a fundamentally different trust model than credibly neutral public infrastructure — and institutional customers should understand that when they sign a commercial agreement with Ant DT, they are not using a trustless system; they are using a highly managed system that inherits Ethereum’s finality but not Ethereum’s censorship resistance.
2. Forced Inclusion
The current architecture has no mechanism for users to submit transactions directly to L1 if the sequencer censors them.[9] Optimistic L2s have fraud proof mechanisms that allow any observer to challenge invalid state but Jovay has no equivalent. The MsgOracle’s 3-of-5 consensus between Jovay and ZAN operators means that if both entities are compromised simultaneously, fraudulent cross-chain messages could be approved.[12]
3. No-Token Decision
Jovayʻs operates with ETH-denominated gas calibrated to Ethereum L1 costs - including base fee, blob fee, and batch/proof transaction costs. Jovayʻs protocol take rate is 1% with the remainder covering Ethereum L1 costs.[19] No native token reduces the securities law risk with Hong Kong regulators. The design points toward a managed, operator-led service model that relies on centralized relayers, privileged roles, and enterprise-facing infrastructure rather than open token incentives or permissionless validator participation.
7. Competitive Landscape
Jovay’s most visible comparators are other Ethereum-linked or institution-facing chains such as Base, Arbitrum, Ink, Arc, and Tempo. But for many of the institutional users it hopes to win, the more important comparison is not another general-purpose L2. It is infrastructure like Canton, which was built specifically for regulated financial markets. [20]
A deep-dive into Canton can be found at the Flashbots Collective “Canton Network Deep Dive”.[26] Canton is built on Digital Asset’s Daml technology stack and was introduced in 2023 with backing from major institutions including Goldman Sachs, BNP Paribas, and Deutsche Börse, alongside more than 30 launch participants. [27] Digital Asset claims the broader Canton ecosystem includes more than 600 institutions and supports more than $6 trillion of on-chain assets across use cases such as bonds, funds, repos, commodities, and insurance.
That scale is visible in repo markets. Broadridge said its distributed-ledger repo platform processed an average of $384 billion in daily repo transactions during December 2025, with nearly $9 trillion in total monthly volume. [28] DTCC has also moved further into tokenization, announcing in December 2025 that DTCC had received SEC no-action relief to offer a tokenization service for select DTCC-custodied assets on pre-approved blockchains in a controlled production environment. The public DTCC announcement does not frame this as an exclusive Canton deployment, so that point should not be overstated. [29]
Fundamentally, Canton and Jovay are designed for different institutional priorities. Canton is optimized for privacy, permissioning, and legal certainty across regulated market participants. Its selective visibility model is well suited to bilateral or multi-party financial workflows such as repo, collateral, and other contracts where transaction confidentiality is central.
Jovay is optimized around a different trade-off. Jovay is an Ethereum-anchored rollup with batch commitments and finality checkpoints on Ethereum, blob-based data availability, TEE-based proof verification in the current design, and centralized sequencing and relaying assumptions. That makes Jovay closer to a publicly anchored but operator-led tokenization stack than to a privacy-first consortium network. [11, 14, 16]
Geography also matters. Cantonʻs strongest current traction is with U.S. and European market infrastructure and capital-market institutions. Jovayʻs traction is more closely aligned with Asia-Pacific tokenization efforts and Hong Kongʻs regulatory push around tokenized assets. Both chains are carving distinct regional and use-case segments of the broader institutional market rather than competing head-to-head for the same customers.
Private permissioned alternatives such as Corda and Hyperledger Fabric also remain part of the competitive set for institutions that do not want any public-chain settlement exposure. Jovayʻs case against those systems is similar to the case for public-chain settlement more broadly: anchoring to Ethereum can offer stronger interoperability, broader composability, and a more publicly auditable settlement layer, but only at the cost of the accepting more public infrastructure exposure and a different trust model. [11]
8. The Biggest Risk: Ant Groupʻs Political Exposure
The core non-technical risk with Jovay is not only its architecture, but also the political and regulatory exposure that comes with being tied to an Ant Group-affiliated stack operating in Hong Kong and China-adjacent markets.
The concern is not hypothetical. Ant Group’s $37 billion IPO was suspended in November 2020 just before listing, with the decision coming from the top levels of Chinese leadership. Following the decision, Ant went through a multi-year regulatory restructuring and was pushed to reorganize as a financial holding company under bank-like capital rules. [29] Jack Ma subsequently gave up control in January 2023, and Chinese regulators imposed a 7.12 billion yuan ($1.1 billion) fine in July 2023 to conclude the rectification process. [30]
For institutions choosing blockchain infrastructure, that history creates a specific dependency risk. Jovayʻs network is deployed across multiple availability zones on Alibaba Cloud and primarily relies on Alibaba Cloud for hosting. [16] Key parts of Jovay are centralized, including the centralized sequencer, operator-controlled permissions, and relayer operation by the operational team.
The message-approval path introduces another concentration point. The Phase 3 audit says all MsgOracle voters are currently operated by the Jovay team, and notes that the design does not include slashing or other economic penalties for malicious voting. In the project team’s own explanation, a compromised voter would not be able to steal funds, but it could delay deposit confirmations. [16]
A geopolitical dispute, a change in Beijing’s technology policy, or regulatory action against Alibaba could affect network availability or operator independence. Jovay and ZAN together control the MsgOracle consensus — if either entity is subject to government-mandated data access or operational interference, the independence of the proof and relaying infrastructure is compromised in ways that a purely cryptoeconomic security model would resist.
9. Why Jovayʻs Architecture Matters
Jovay is not trying to win the race for the best general-purpose L2. It is trying to build Ethereum-anchored settlement infrastructure for regulated tokenization in Asia. To do that, Jovay has made a distinct set of architectural bets:
- TEE-based verification is acceptable enough for early institutional adoption while ZK proving matures. Today, Jovayʻs rollup supports TEE proofs in production, while ZK verification hooks exist in the codebase and are not yet active. [11]
- Centralized sequencing and operator control may matter more to regulated institutions than permissionless decentralization. Jovayʻs current design relies on trusted relayers, privileged owners, and a centralized sequencing model rather than open validator participation. [11, 16]
- Vertical integration across compliance, issuance, and settlement may be a stronger competitive moat than any single technical component.
- Hong Kongʻs policy support for tokenization gives Jovay a favorable local environment. The city has expanded tokenized bond issuance, advanced project Ensemble into real-value pilots, and continued joint HKMA-SFC work on tokenized assets. [3, 4, 5, 6]
The broader implication is that institutional blockchain infrastructure may not converge on a single design.
- Canton is building privacy-oriented infrastructure for regulated US/European financial markets, especially where institutions want interoperability without giving up privacy and control.
- Jovay is building an Ethereum-anchored, operator-led rollup for Asia-Pacific tokenization under local regulatory conditions.
- Arc is stablecoin-native L1 designed around predictable fees, deterministic settlement, and direct integration with Circle’s stack.
- Tempo is a payments-first blockchain optimized for stablecoins, with dedicated payment-oriented features and a roadmap toward permissionless decentralization.
- Private Corda/Fabric deployments are still likely to persist where enterprises do not want public-chain settlement exposure at all.
Multiple blockchain architectures may coexist, each optimized for a different combination of jurisdiction, use case, and institutional trust model.
10. Open Questions
1. ZK transition is unresolved
Jovay’s entire trust model improvement depends on moving from TEE-based verification to cryptographic validity proofs. Today, the system verifies TEE attestations on-chain, while ZK verification hooks exist in the codebase but are not yet active. That means institutions are relying on Intel DCAP attestation, trusted measurement configuration, and operator integrity rather than end-to-end cryptographic validity proofs. Until a production ZK path is live, “validity rollup” should be treated as a roadmap goal and not a current security property.
2. Sequencer decentralization remains undefined
Jovay currently operates with a centralized sequencer and operator-controlled relaying rather than a decentralized validator or a sequencer set. There are plans for future decentralization but no concrete public mechanism, governance process, or timeline for how sequencing becomes less centralized. This is commercially acceptable for Jovayʻs current institutional model, which looks more like a managed service than a neutral public utility. But it creates a long-term ceiling on credible neutrality that may matter more as the asset base grows and the network’s systemic importance increases.
3. The AntChain Bridge trust model is underspecified
The technical documentation does not fully explain the trust assumptions behind the separate AntChain-to-Jovay bridge, or the “Dual Chains and One Bridge”. That leaves an important open question: when assets or state move from a private AntChain deployment to public Jovay, what exactly is being trusted, verified, and relayed? If state from a private chain can influence public settlement, the bridge design deserves a more explicit disclosure of its verification path, operator roles, and failure assumptions.
4. Fee competitiveness at scale
Jovayʻs fee model deserves more scrutiny as institutional transaction volumes grow. Jovay calibrates its L2 fees using Ethereum L1 base fee, blob fee, and actual batch/proof costs. Jovay takes a fixed 1% protocol spread. [19] Arc and Tempo are clearly positioning around more predictable institutional fee, with Arc using USDC as gas and Tempo allowing fees to be paid directly in stablecoins. For high-frequency institutional trading, the use case that Jovayʻs performance benchmarks are targeting, a 100x fee premium relative to competing L2s is a material commercial question. The real question is whether Jovayʻs managed-service model and bundled issuance/compliance stack justify higher total cost for the institutional workflows it targets.
5. Liquidity without DeFi
Tokenized assets on Jovay may face a familiar trade-off: the compliance controls that make the network attractive to issuers can also limit broad composability and open secondary-market liquidity. That does not prevent institutional trading, but it does raise a harder question about where sustained liquidity comes from if the network is not relying on open DeFi venues. In practice, the key adoption challenge may be less issuance and more whether Jovay can support compliant secondary markets with enough depth, counterparties, and market infrastructure to matter at institutional scale.
Resources
[1] Towngas. Towngas Completes First Real-world Asset Tokenization Project. Nov. 2025.
[2] Binance. Jovay Transforms Green Finance! 14 Million Devices Connected on Chain Sprinting Globally. 2025.
[3] Hong Kong Monetary Authority. HKMA Launches Project Ensemble Sandbox to Accelerate Adoption of Tokenisation. August 28, 2024.
[4] Hong Kong Monetary Authority. HKMA Announces the New Phase of Project Ensemble — EnsembleTX. November 13, 2025.
[5] Hong Kong Securities and Futures Commission. Joint Circular on Intermediaries’ Virtual Asset-related Activities. SFC, 2024.
[6] Hong Kong Monetary Authority. Regulatory Sandbox for Tokenized Deposits. HKMA, 2024.
[7] Ethereum Foundation. Optimistic Rollups.
[8] Ant DT Technologies. Jovay Technical Whitepaper v1.0. Jovay Network, 2025.
[9] OpenZeppelin. Jovay Solidity Sequencer Audit. 15 Oct. 2025.
[10] Jovay Network. Jovay Network Documentation. Jovay Network, 2025.
[11] OpenZeppelin. Jovay Solidity Rollup Audit. 15 Oct. 2025.
[12] Zellic. Jovay Relayer Application Security Assessment. 22 Dec. 2025.
[13] Ant DT Technologies. ZAN Platform Documentation. Ant DT, 2024.
[14] OpenZeppelin. Jovay TEE Verifier Audit. 14 Oct. 2025.
[15] Costan, Victor, and Srinivas Devadas. Intel SGX Explained. Cryptology ePrint Archive, 2016.
[16] SlowMist. Jovay Network Chain Security Audit Report. 24 Sept. 2025.
[17] Jovay Research Team. Packed Sumcheck over Fields of Small Characteristic. Advances in Cryptology — ASIACRYPT 2025, 2025.
[18] EIP-4844: Shard Blob Transactions. Ethereum Improvement Proposals.
[19] Edward Liu, Product Manager – Jovay Network.
[20] Edward Liu, Product Manager — Jovay Network, and Alexandra Wang, Business Development — Jovay Network, interview by Tesa Ho. Consensus Hong Kong, 19 Feb. 2026.
[21] Zhou et al. DTVM: Revolutionizing Smart Contract Execution with Determinism and Compatibility. 9 June 2025.
[22] Github. DTVM Stack.
[23] Ant DT Technologies. Ant DT Technologies Introduces DT Tokenization Suite, a Full-Stack Tokenization-as-a-Service. Ant DT, 2025.
[24] Ant DT Technologies. AntChain Bridge. Ant DT, 2025.
[25] Ant DT Technologies. TopNod. Ant DT, 2024.
[26] The Flashbots Collective. Canton Network Deep Dive. Jan. 2026.
[27] Canton Network. Introducing the Canton Network. Digital Asset, May 2023.
[28] CoinDesk. Wall Street Heavyweights Back Builder of Canton, a Network That Supports $6T Onchain Assets. December 4, 2025.
[29] DTCC. DTCC to Use Canton Network to Tokenize US Treasury Securities. December 2025.
[30] Reuters. Ant Group Founder Jack Ma to Give Up Control in Key Revamp. January 7, 2023.
[31] CNBC. China to End Ant Group’s Regulatory Revamp with Fine of at Least $1.1 Billion. July 7, 2023.